Would You Click The Links In This Email?
/Scammers are notorious for sending fraudulent emails that appear to come from reputable parties. The longer they've been at it, the better they've gotten. So it's easy for a person to make an honest mistake and click a link in what they think is a legitimate email from a legitimate source. Unfortunately, doing so may mean that the recipient is tricked into giving up sensitive information (such as a username and password) or downloading malware onto their computer.
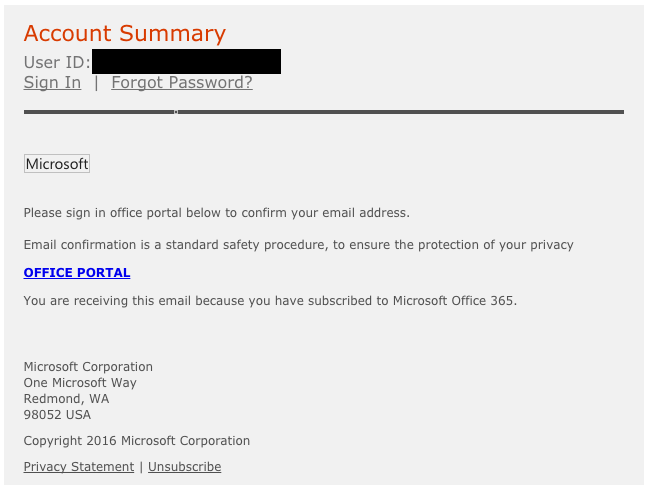
One of the best lines of defense against the threat of fraudulent emails impacting your organization is to raise awareness, which has become a key component of a holistic cybersecurity strategy. To help you get started, here's a test. Take a look at the email below, which was sent from the email address office@365.com. The "User ID," which is blacked out, was the recipient's email address.
Would you click the links in this email?
What do you think? The recipient did have an Office 365 account. And this looks like an official communication, with a business address, a privacy statement, and even an "unsubscribe" option. Take a moment to decide before scrolling down to find the answer.
The answer is no: you should not click on links in this email. But chances are, on a busy day with an inbox full of emails to get through, you just might simply click out of habit.
So let's take a closer look at this email. While it certainly has elements that look legitimate, it also has at least two of the major hallmarks of scam emails:
1. Bad Links
If you hover your cursor over a link in most web browsers or email clients, you should see the URL behind that link displayed, usually in the lower, left-hand corner of the window. In the case of the email above, hovering over any of the links revealed this URL:
As you can see, the web address behind the links is not associated with Microsoft or Office 365, despite the content of the email and anchor text of the links. This is a red flag that the email is fraudulent. If the recipient clicked the link, they may have been directed to a website made to look like a user portal for Office 365, and tricked into entering (and thus compromising) their email address and password. Or, the website behind the link may have automatically tried to download malware onto the recipient's system.
At any rate, it's important to look at links closely. In this particular case, it's obvious that the web address has nothing to do with the purported sender. In some cases, though, scammers use web addresses that look similar to legitimate ones.
2. Bad Timing
While some vendors do ask for email verification when you create a new account with them, it's not at all common for them to request verification after an account has been up and running for a while. The recipient of this email did have an Office 365 account, but it had been set up long before he received the email. So, it didn't make sense for the recipient to get the email when he did, which is another red flag.
The point is that spotting fraudulent emails involves stopping and thinking about the sender and the reason they claim to be sending the information. It's easy just to click and follow directions, especially when the email in question relates to an important account. But it's best practice to stop and think before clicking anything in any email. And if you have any level of doubt about an email, always contact an IT professional, or reach out to the vendor directly.
Have questions, or an even better example of an email scam? Give us a call, or post in the comment section below.
And don't forget to share this post with employees, coworkers, or friends to spread awareness!